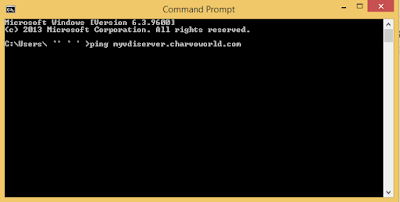
Check you able to ping VDI Server from client device
Ping myvdiserver. you need to ping VDI connection server IP.
Try this batch script
==========================================================
@echo off
set /p host=VDI Server URL:
set logfile=Log_%host%.log
echo Target Host = %host% >%logfile%
for /f "tokens=*" %%A in ('ping %host% -n 1 ') do (echo %%A>>%logfile% && GOTO Ping)
:Ping
for /f "tokens=* skip=2" %%A in ('ping %host% -n 1 ') do (
echo %date% %time:~0,2%:%time:~3,2%:%time:~6,2% %%A>>%logfile%
echo %date% %time:~0,2%:%time:~3,2%:%time:~6,2% %%A
timeout 1 >NUL
GOTO Ping)
=========================================================
Create batch file and run it. you will see command prompt open as shown below.
Enter Connection server IP or FQDN and Enter
It will show below mentioned like response. Note : Good network should have stable communication and non disturb of communication. Means it ping latency should be stable which should be less 50ms more than that will impact you VDI desktop performance.
Or
Try other batch script
==========================================================
@echo off
for /f "tokens=*" %%A in ('ping <ip_Address> -n 1 ') do (echo %%A>>pinglog.txt && GOTO Ping)
:Ping
Timeout /t 1 >nul
for /f "tokens=* skip=2" %%A in ('ping <ip_Address> -n 1 ') do (echo %date% %time% %%A>>pinglog.txt && GOTO Ping)
============================================================
just run this script and it will create file pinglog.txt and don't forget to mention ip address in <ip_address> in script.
Port Check
View Connection/Security servers are usually deployed in DMZ and acts as proxy for horizon view clients. As a best practices for both Security Servers and Connection Servers is to keep the Windows Firewall turned on. During the install process the installer notifies you that your firewall isn’t On. The installer opens the ports during install.
If the firewall on either server is turned off, View will not be able to use IPSEC when communicating. Security servers has to be paired with connection servers. Static IP is a requirement here.
The front-end security servers needs to have following ports opened:
HTTP Ports
80 (TCP)
- The port 80 TCP must be open in only the inbound direction.
HTTPS Ports
443 (TCP)
- The port 443 TCP must be open in only the inbound direction.
PCoIP Ports
4172 (TCP/UDP)- Used for PCoIP in a VMware View 4.5 and later environment. This port is required for the PCoIP display protocol.
- The port 4172 UDP must be open in both inbound and outbound directions.
- The port 4172 TCP must be open in only the inbound direction.
Even if planning small deployment, the View Connection Server must be installed on its own dedicated server. It must NOT be installed on the vCenter server or a domain controller. So the smallest view infrastructure needs four components:
ESXi
vCenter
View Connection Server
Active Directory
Key Firewall Considerations for VMware Horizon 6
- TCP 8472: View interpod API (Cloud Pod Architecture) – NEW
- TCP 22389: Global ADLDS (Cloud Pod Architecture) – NEW
- HTTPS (443): Horizon Client access, authentication and RDP tunnel (HTTPS Secure Gateway)
- HTTPS (8443): Used by HTML Access (Blast)
- HTTPS (22443): HTML Access (Blast) to Virtual Desktops
- TCP 9427: Used by Windows multimedia redirection (MMR)
- TCP 32111: USB Redirection
- ESP (Protocol 50) used for Security Server and Connection Server IPSEC communication (requires Windows firewall with Advanced Security to be enabled)
- UDP 500: IPsec negotiation for Security Server and Connection Server communication and pairing.
VMware horizon View 6 documentation links:
- Firewall Rules for View Connection Server
- Firewall Rules for View Agent
- Firewall Rules for Active Directory



Comments
Post a Comment